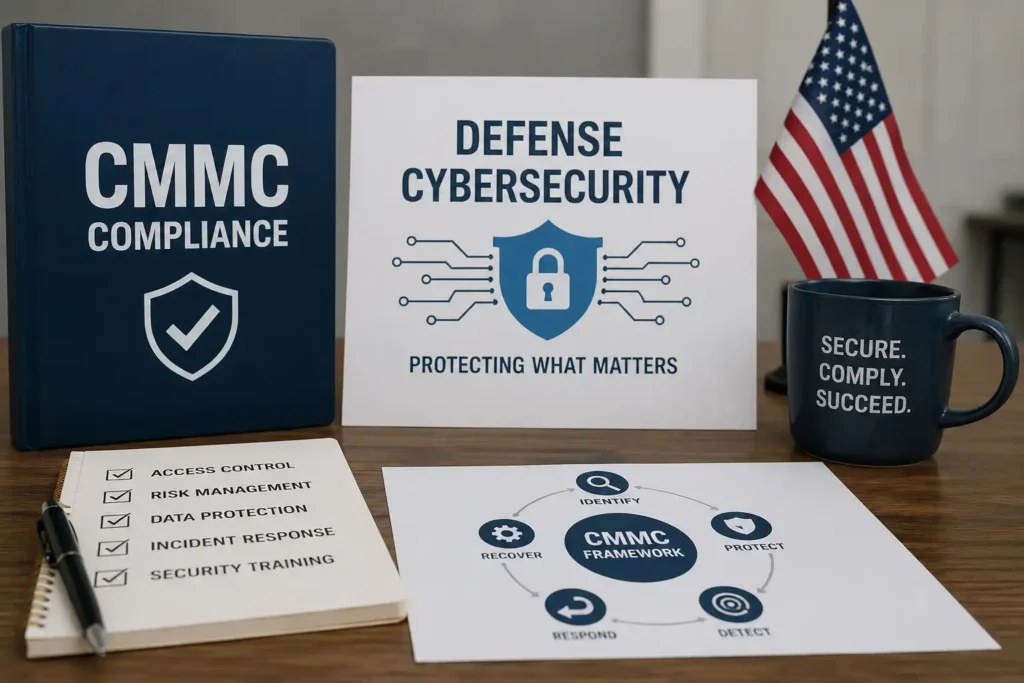
CMMC Solutions: How Small Businesses Can Navigate Defense Cybersecurity Requirements
The Cybersecurity Maturity Model Certification (CMMC) has fundamentally reshaped how defense contractors approach data security. Developed by the Department of Defense to address persistent vulnerabilities in the defense industrial base, CMMC establishes tiered cybersecurity standards that companies must meet to bid on government contracts. For small businesses, these requirements represent both a significant compliance challenge and a competitive necessity failure to achieve certification means exclusion from lucrative defense work.
At its core, CMMC builds upon the National Institute of Standards and Technology’s Special Publication 800-171, which outlines security requirements for protecting Controlled Unclassified Information (CUI) in non-federal systems. As NIST’s cybersecurity framework continues to evolve in response to emerging threats, small businesses face mounting pressure to implement enterprise-grade security measures despite limited budgets and technical expertise. The stakes are particularly high: a single breach can compromise national security interests while destroying a company’s reputation and contract pipeline.
What NIST Compliance Actually Requires
NIST SP 800-171 establishes 110 security controls across 14 families, ranging from access control and incident response to system integrity and personnel security. These requirements aren’t merely bureaucratic checkboxes they represent fundamental protections against the sophisticated threat actors targeting defense supply chains. Companies handling CUI must implement technical safeguards like multi-factor authentication and encryption, while also establishing administrative controls, including security policies and employee training programs.
The compliance mandate extends beyond prime contractors to subcontractors at every tier. Any organization that processes, stores, or transmits CUI on behalf of the government must demonstrate adherence to these standards. This cascading requirement has created urgency throughout the defense industrial base, particularly among smaller firms that previously operated with minimal cybersecurity infrastructure.
💚 You might also like: How Data-Driven Insights Are Transforming Interview Preparation
The Path to CMMC Compliance for Small Businesses
Achieving CMMC certification requires methodical preparation and often significant operational changes. Small businesses should approach compliance as a structured project rather than a one-time audit preparation effort:
- Conduct a Gap Assessment: Document your current security posture against CMMC requirements to identify deficiencies. This baseline assessment reveals which controls are missing, partially implemented, or inadequately documented.
- Determine Your Required Level: CMMC includes three levels of certification, with Level 2 (aligned with NIST 800-171) required for most contractors handling CUI. Understanding your contractual obligations prevents over-investment in unnecessary controls.
- Develop a Remediation Roadmap: Prioritize gaps based on risk and implementation complexity. Quick wins like policy documentation can proceed while you plan more substantial infrastructure upgrades.
- Engage Specialized Expertise: Many small businesses work with consultants who specialize in defense cybersecurity requirements. Firms offering streamlined CMMC compliance solutions such as Cuick Trac, Redspin, and Coalfire have developed approaches that reduce the burden on resource-constrained organizations.
- Implement Technical and Administrative Controls: Execute your remediation plan, updating network architecture, deploying security tools, revising policies, and training personnel. Documentation is critical assessors will require evidence that controls are both implemented and effective.
- Establish Continuous Monitoring: Compliance isn’t static. Implement processes to maintain security controls, track system changes, and respond to new vulnerabilities as they emerge.
- Prepare for Third-Party Assessment: CMMC Level 2 requires certification by an accredited assessor. Conduct internal audits to identify remaining gaps before the formal assessment.
The timeline from initial assessment to certification typically spans six to twelve months, depending on a company’s starting point and available resources. Rushing the process often results in failed assessments and wasted investment.
Core NIST 800-171 Compliance Solutions
Meeting NIST 800-171 requirements demands a combination of technology, processes, and organizational commitment. The most effective compliance programs integrate multiple layers of protection:
- Data Encryption: Protect CUI both at rest and in transit using FIPS 140-2 validated cryptographic modules. This includes encrypting laptops, mobile devices, backup media, and network communications.
- Identity and Access Management: Implement least-privilege access controls, multi-factor authentication, and regular access reviews. Only personnel with legitimate business needs should access CUI.
- Network Segmentation and Monitoring: Deploy firewalls, intrusion detection systems, and security information and event management (SIEM) tools to identify and respond to threats. Network segmentation limits the blast radius of potential breaches.
- Security Awareness Training: Human error remains the leading cause of security incidents. Regular training helps employees recognize phishing attempts, social engineering, and other common attack vectors.
- Incident Response Capabilities: Develop and test procedures for detecting, containing, and recovering from security incidents.
- Vulnerability Management: Establish processes for identifying, prioritizing, and remediating security vulnerabilities in systems and applications. This includes timely patching and configuration management.
- Regular Security Assessments: Conduct periodic audits and penetration tests to validate control effectiveness and identify emerging risks before they’re exploited.
These solutions require ongoing investment and attention. Companies that treat compliance as a one-time project rather than a continuous program inevitably fall out of compliance and face certification challenges.
💚 You might also like: How AI Compliance Helps Businesses Meet Regulatory Requirements
Building a Secure CUI Enclave
A CUI enclave is a segregated environment specifically designed to process, store, and transmit controlled unclassified information. This architectural approach allows businesses to concentrate security investments on systems that actually handle sensitive data, rather than securing their entire IT infrastructure to CMMC standards.
Effective enclave design incorporates several critical elements:
- Physical and Logical Separation: Isolate CUI systems from general business networks through firewalls, VLANs, or air gaps. This containment strategy limits the scope of compliance requirements and reduces the attack surface.
- Strict Access Controls: Implement role-based access with multi-factor authentication. Only cleared personnel with specific job requirements should access the enclave.
- Comprehensive Encryption: Encrypt all data within the enclave using approved cryptographic standards. This includes data at rest on servers and workstations, as well as data in transit across networks.
- Continuous Monitoring: Deploy logging and monitoring tools that capture security-relevant events. Regular review of these logs helps detect anomalous activity that might indicate a breach.
- Regular Security Assessments: Conduct vulnerability scans and penetration tests focused specifically on the enclave environment to identify weaknesses before adversaries do.
While enclaves reduce the scope of CMMC compliance, they introduce operational complexity. Employees must understand which systems contain CUI and follow appropriate handling procedures a challenge that requires clear policies and ongoing training.
Practical Cybersecurity Solutions for Resource-Constrained Businesses
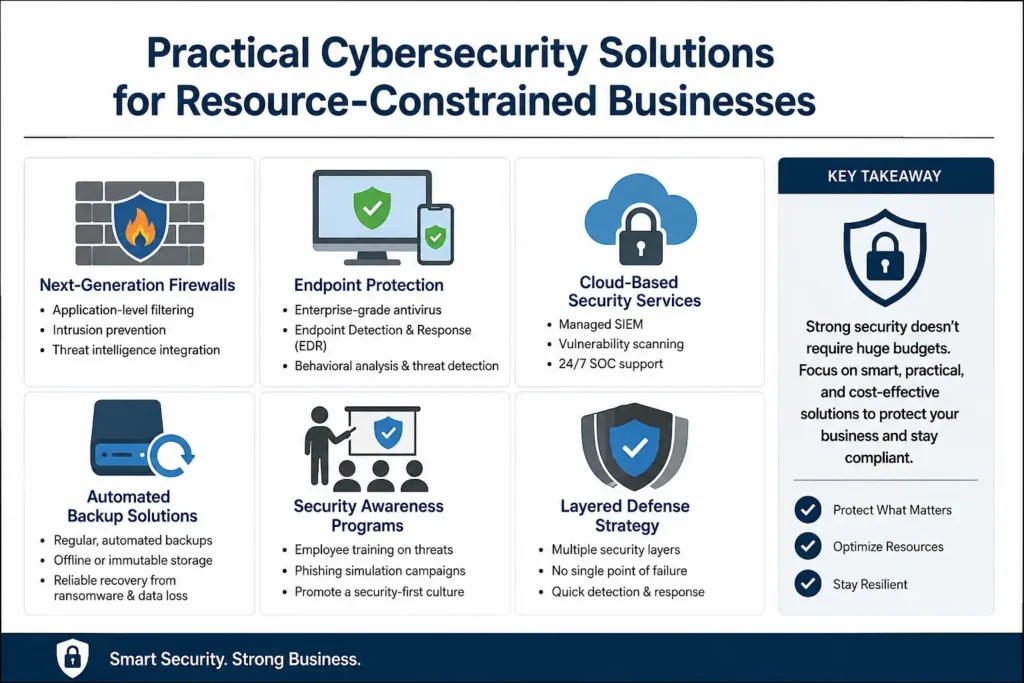
Small businesses face unique cybersecurity challenges: limited budgets, minimal IT staff, and competing operational priorities. Yet the threat landscape doesn’t discriminate by company size. Small businesses are frequent targets precisely because attackers perceive them as easier to compromise.
Effective cybersecurity for small businesses focuses on high-impact, cost-effective measures:
- Next-Generation Firewalls: Modern firewalls provide application-level filtering, intrusion prevention, and threat intelligence integration capabilities that were once available only to large enterprises.
- Endpoint Protection: Deploy enterprise-grade antivirus and endpoint detection and response (EDR) tools across all devices. These solutions use behavioral analysis and machine learning to identify threats that signature-based tools miss.
- Cloud-Based Security Services: Managed security service providers offer enterprise capabilities at small business prices. Services like managed SIEM, vulnerability scanning, and security operations center (SOC) support provide expertise that would be prohibitively expensive to build in-house.
- Automated Backup Solutions: Implement regular, automated backups with offline or immutable storage. Ransomware attacks have crippled countless small businesses that lacked reliable backup and recovery capabilities.
- Security Awareness Programs: Invest in regular training that teaches employees to recognize and report suspicious activity. Simulated phishing campaigns help reinforce these lessons and identify individuals who need additional coaching.
The key is building layered defenses that don’t depend on any single control. When one protection fails and eventually something will, other controls should contain the damage and provide time to respond.
💚 You might also like: The Role of Proxy Testing in Modern Network Management
Your NIST Compliance Checklist
Navigating NIST 800-171 requirements can feel overwhelming, particularly for organizations new to defense contracting. This checklist provides a structured approach to achieving and maintaining compliance:
- Understand the Requirements: Review NIST SP 800-171 in detail, focusing on the 110 security controls and their implementation guidance. Don’t rely solely on summaries the nuances matter during assessments.
- Scope Your CUI Environment: Identify all systems, networks, and personnel that process, store, or transmit CUI. Accurate scoping is essential for determining which assets must meet NIST requirements.
- Perform a Comprehensive Risk Assessment: Document threats, vulnerabilities, and potential impacts to your CUI environment. This assessment informs your security control selection and implementation priorities.
- Develop a System Security Plan: Create detailed documentation describing your security controls, implementation approach, and responsibility assignments. This living document serves as your compliance roadmap and evidence during assessments.
- Implement Required Security Controls: Deploy technical controls (encryption, access management, network security) and administrative controls (policies, procedures, training) across your CUI environment.
- Document Everything: Maintain evidence of control implementation and effectiveness. Assessors will require proof that controls are not just deployed but actually functioning as intended.
- Train Your Workforce: Ensure all personnel understand their security responsibilities, particularly those who handle CUI. Document training completion and conduct refresher sessions regularly.
- Establish Continuous Monitoring: Implement processes to track system changes, monitor for security events, and maintain control effectiveness over time. Compliance is an ongoing state, not a one-time achievement.
- Conduct Internal Audits: Regularly assess your compliance posture through self-assessments or third-party audits. Identifying and remediating gaps proactively is far less costly than failing a formal CMMC assessment.
- Develop a Plan of Action and Milestones (POA&M): Document any security control deficiencies along with remediation plans and timelines. Assessors expect to see POA&Ms for controls that aren’t fully implemented.
This checklist represents a significant undertaking, but systematic execution makes the process manageable. Many small businesses find that breaking the work into phases, starting with quick wins and gradually addressing more complex requirements, maintains momentum while demonstrating progress to leadership and customers.
✨ Got value? Let’s keep the momentum, follow Tech Statar.

















![Software Perchance AI Image Generator: A Comprehensive Guide [2025]](https://techstatar.com/wp-content/uploads/2025/10/1750759678367-perchance-ai-review.jpg)