Ten Kilobytes Against a City: V2X Sabotage
Traffic lights do not look like weapons. They hang at intersections, blinking through their cycles, quietly governing the daily movement of lives. But to an embedded systems engineer who knows what runs inside a roadside V2X unit, those same lights look like something else: open ports, legacy firmware, and a communication stack built for speed.
The cities now wiring themselves with V2X sensors and adaptive traffic systems are building more than convenience infrastructure. Over the past decade, firms providing embedded software development services for mobility portals have constructed connections that now span entire cities. The embedded software engineering work behind these platforms creates, by design, a mesh of addressable nodes spread across every major road. Firms like N-iX have moved into this space, developing the low-level software stacks that sit between sensors and city management platforms. The exposure that comes with that connectivity is rather architectural than theoretical.
A recent ENISA Threat Landscape report found that attacks on transportation infrastructure rose sharply across EU member states, with smart mobility systems identified as an emerging category of interest for both criminal and state-linked actors.
The Geometry of a Gridlock Attack
Picture a city’s V2X network as a nervous system. Each Roadside Unit (RSU) is a node, broadcasting over C-V2X or DSRC protocols to vehicles within roughly 300 meters, exchanging signal phase data, speed advisories, and hazard alerts. Under normal operation, this is elegant. Cars slow down before they see a red light. Emergency vehicles get green corridors without a dispatcher making a single call.
Now picture someone who has found a mundane vulnerability in a commercial RSU, not a zero-day, just a predictable memory allocation error in the V2X protocol stack, the kind that accumulates in embedded firmware when development timelines are short and safety-critical testing gets quietly dropped. Ten kilobytes, sent over the air.
The RSU crashes. Or it starts broadcasting false signal data. Sometimes that second outcome is worse.
In isolation, one compromised node causes a minor delay. But modern traffic management systems are not isolated. They share data and defer to upstream coordinators, adjusting their cycles based on network-wide state. Cascade one RSU failure into a cluster, and the city’s arterials start to seize, the system making decisions from corrupted inputs while every light above ground looks fine, with the kind of deniability that makes attribution nearly impossible.
Researchers have a name for this now. They call it a Gridlock Attack. It requires no equipment, and no one needs to leave their desk.
C-V2X Security and the Developer’s Dilemma
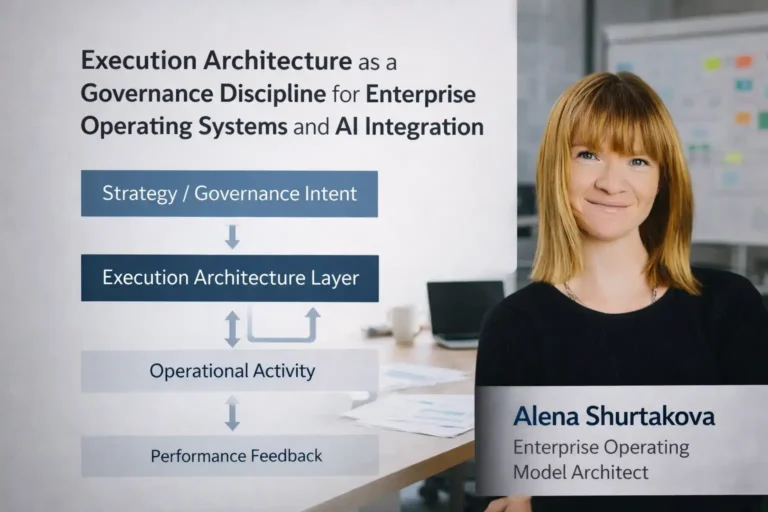
The embedded developers building these systems are not careless. Most work under strict automotive standards, including ISO 21434 and UNECE WP.29, fully aware that vehicular software carries physical consequences. But standards do not write code. They describe what should happen. The gap between a well-intentioned security requirement and a correctly implemented cryptographic handshake in a constrained embedded environment is where most real-world vulnerabilities actually live.
A few pressure points that keep recurring in deployed systems:
- Certificate revocation in V2X PKI is slow, sometimes taking hours to propagate across a city’s RSU network, leaving a window for replay attacks using compromised credentials that have not yet been revoked.
- Many deployed RSUs run on hardware with limited secure-boot support, meaning firmware updates can be spoofed if signing verification is incomplete.
- The C-V2X standard specifies message authentication but does not mandate how frequently receiving systems must verify messages, leaving that implementation detail to each embedded development team.
These are not exotic problems. They are the kind of decisions that get made on a Tuesday afternoon when a senior engineer is reconciling a real-time processing budget with a security requirement written by a committee that never had to hit a 50-millisecond latency target.
NHTSA assessment of connected vehicle incidents found that most security failures involved implementation-level errors rather than specification gaps, which makes clear that how embedded code is written matters as much as what it is supposed to do. The companies now providing embedded software development for smart city and automotive clients carry a specific responsibility, the code they ship runs inside a city, not a product spec.
The Digital Border
There is a phrase some embedded security researchers have started using: “digital border.” It refers to the perimeter a city can draw, or fail to draw, around its own physical movement. When every intersection is addressable, every traffic pattern becomes a potential control surface. Block the arterials, and an emergency vehicle takes nine minutes to cover a distance it normally handles in three. Choke a highway on-ramp during an evacuation, and a city loses its ability to move itself to safety, stopped by a compromised RSU and some well-timed broadcast packets.
Criminal actors have noticed. IBM’s analysis of cyberthreats in 2026 documented growing interest in transportation control systems, including early-stage reconnaissance against smart mobility platforms in North America and Western Europe.
The firms delivering embedded systems development work for automotive and smart city clients are, effectively, building that border. Whether it holds depends on decisions made during code review and on the painstaking work of threat-modeling scenarios that may never materialize but carry a real cost if they do.
N-iX, operating in the embedded firmware and automotive software space, is one of those firms navigating this terrain. So are dozens of others. The work is not glamorous. Interrupt handlers and V2X protocol parsers rarely show up in marketing decks. But embedded software development work shapes what a city can do in a crisis, which is another way of saying it shapes the city itself.
Conclusion
The vulnerability in a traffic sensor is not the interesting part. Everything that becomes possible once it is found, that is where the real story lives. A city’s movement is its life, and the engineers writing the embedded code that governs it are, whether they want the title or not, its most quietly consequential defenders. Smart cities can be attacked; that much is settled. Whether the teams building their digital borders get the time and rigor to make those attacks genuinely hard, that is the question still waiting for an answer.
✨ More clarity. More insights. Less noise. Follow Tech Statar.